Table of Contents
ToggleU.S. ALLOWS INDIA TEMPORARY RUSSIAN OIL IMPORTS
TOPIC: (GS2) INTERNATIONAL RELATIONS: THE HINDU
The U.S. Treasury Department issued an order permitting India to import Russian oil for 30 days to ease supply shocks caused by Iran’s blockade of the Strait of Hormuz and rising global crude prices.
Need for Russian Oil
- Over 55% of India’s oil imports pass through the Strait of Hormuz.
- Disruptions raise India’s monthly oil bill (~$11.5 billion).
- If Brent crude crosses $90 per barrel, India’s CAD could rise to 1.4% of GDP and the rupee may weaken to ₹95 per U.S. dollar.
- Russian imports are seen as a buffer against price volatility.
Key Developments
- Temporary Relief: U.S. Treasury Secretary Scott Bessent said the measure is shortterm and applies only to oil already stranded at sea.
- Market Impact: Brent crude prices surged to $88 per barrel, up 20% in a week.
- India’s Reserves: Government confirmed India has 25 days of crude oil, petrol, and diesel reserves.
- Russian Oil Discount: Officials noted Russian oil may no longer be available at a discount, as China is also competing for supplies.

Import Trends:
- India imported $1.98 billion worth of Russian crude in Jan 2026, the lowest in 44 months.
- Russia’s share in India’s oil imports fell to 19.3% in Jan 2026, compared to 27.5% in Nov 2025 and 33% in May 2025.
- Current imports: 1.04 million barrels/day from Russia.
Economic Concerns
- Moody’s Analysis: India is highly dependent on West Asian crude.
- Costly imports could weaken the rupee, raise inflation, worsen CAD, and complicate fiscal management.
- Policy Pressure: India faces U.S. pressure to reduce Russian imports while balancing domestic energy needs.
Ratio of Oil Imports by Country
- Russia: 19.3%
- West Asia (Saudi Arabia, Iraq, UAE, etc.): ~55%
- United States & Others: Growing share, replacing part of Russian imports
Conclusion
The U.S. waiver provides India shortterm relief amid global energy disruptions. Diversifying energy sources and strengthening reserves remain critical for energy security and economic stability.
GOVERNOR AND LIEUTENANT GOVERNOR APPOINTMENT IN INDIA
TOPIC: (GS2) POLITY: THE HINDU
President Droupadi Murmu recently announced a reshuffle of Governors and Lieutenant Governors across several states and union territories.
Governor
- Article 153: Every state must have a Governor.
- Article 155: Appointed directly by the President of India through a warrant under hand and seal.
- Article 156: Holds office during the pleasure of the President; standard term is five years.
- Article 157: Must be an Indian citizen and at least 35 years old.
- Article 158: Cannot be a member of Parliament/State Legislature or hold any office of profit.
- Article 159: Takes oath administered by the Chief Justice of the High Court.
- Conventions:
- Usually appointed from outside the state to ensure neutrality.
- Consultation with Chief Minister is expected but not mandatory.
Lieutenant Governor – Appointment Process
- Article 239: Union Territories are administered by the President through an Administrator.
- Designation: In Delhi, Puducherry, J&K, Ladakh, and Andaman & Nicobar Islands, the Administrator is called Lieutenant Governor (LG).
- Article 239AA: Specifically provides for LG in Delhi.
- Appointment: Directly by the President, on advice of the Union Council of Ministers.
- Term: Holds office during the pleasure of the President, similar to Governors.
Why Governors are Appointed, Not Elected
- Prevents conflict with Chief Minister (avoids dual power centres).
- Governor is a nominal head, while CM is the real executive.
- Ensures national unity and acts as a link between Centre and State.
- Maintains neutrality of office, avoiding political bias.
Key Commission Recommendations
- Sarkaria Commission (1983): Eminent person from outside the state; consult CM, VicePresident, and Speaker before appointment; avoid premature removal.
- Venkatachaliah Commission (2002): Governors should normally complete fiveyear term; consult CM if removed early.
- Punchhi Commission (2007): Suggested deleting “pleasure of President” clause; removal only through resolution of state legislature.
Conclusion
The Governor and LG are crucial constitutional authorities ensuring Centre–State coordination and stability. While their appointment process is rooted in neutrality, debates continue on reforming tenure security and consultation mechanisms to strengthen India’s federal structure.
BALANCING INNOVATION WITH WOMEN’S DIGITAL SAFETY
TOPIC: (GS2) POLITY: THE HINDU
On International Women’s Day 2026 (March 8), discussions around ethical AI and women’s digital safety gained prominence. Rising cases of online harassment, deepfakes, and AI misuse highlight the urgent need for stronger safeguards.
Importance of Women in AI Development
- Diverse Viewpoints: Inclusion of women researchers can shape technology to reflect lived experiences.
- Safer Platforms: More representation ensures AI tools are designed to swiftly remove harmful content.
- UN Women’s Proposal: Greater participation of women in AI research can profoundly influence the foundations of technology.
Digital Threats Faced by Women
- High Prevalence: Studies show 16%–58% of women face online abuse and harassment.
- Beyond Physical Boundaries: Abuse now extends into the digital world through anonymity and technology.
- Deepfake Era: AIgenerated fake images and videos (e.g., Grok AI misuse) are being weaponised against women.
Key Concerns
- Anonymity of Perpetrators: Online platforms make it difficult to identify and punish offenders.
- Lack of Representation: Women form only 22% of AI professionals and less than 14% in senior roles, limiting diverse perspectives in AI design.
- Bias in AI Tools: Many deepfake technologies disproportionately target women, reflecting gender imbalance in development.
Way Forward
- Strengthen Legal Enforcement: Ensure strict implementation of cyber laws with fasttrack investigation and penalties for online abuse, deepfakes, and harassment.
- Promote Digital Literacy & Awareness: Conduct awareness campaigns to help women identify, report, and protect themselves from online threats.
- Inclusive Technology Development: Invest in tools that can detect and block harmful content quickly, making digital spaces safer.
Government Initiatives
- IT Ministry Guidelines (2024–25): Online intermediaries are required to remove deepfake content within 3 hours of receiving a takedown notice.
- National Cyber Crime Reporting Portal: Provides a platform for victims to report cyber harassment, stalking, and online abuse.
- Digital India Programme: Promotes safe internet use, digital literacy, and awareness campaigns, especially targeting women and children.
Legal and Policy Measures
- Indian Guidelines: Ministry of Electronics and IT mandates removal of deepfake content within 3 hours of notice.
- Need for Stronger Laws: Prompt investigations and stricter enforcement are essential to protect women from irreparable harm.
- Global Push: Ethical AI frameworks must integrate gendersensitive safeguards.
Conclusion
AI and digital innovation are inevitable, but without ethical safeguards, women risk bearing the brunt of technological misuse. Ensuring representation of women in AI development, stronger legal frameworks, and early digital education are crucial steps to balance innovation with safety.
RIGHTS, JUSTICE, AND ACTION FOR INDIA’S WOMEN FARMERS
TOPIC: (GS2) POLITY: THE HINDU
On International Women’s Day 2026 (March 8), International Year of the Woman Farmer, the theme focuses on equal rights and justice for women farmers.
Women Farmers in India
- Workforce Share: Women make up 42% of India’s agricultural workforce. Over 55% of female main workers are agricultural labourers, while 24% are cultivators (Census 2011).
- Land Ownership: Despite reforms, only about 12–13% of rural women own land titles.
- Contribution to Agriculture: Women contribute 60–70% of labour in food production, including sowing, weeding, harvesting, and postharvest work.
- Their share in agricultural Gross Value Added (GVA) is estimated at around onethird
Feminisation of Agriculture
- Migration Impact: With men migrating, women increasingly shoulder cultivation, risk management, and household food provisioning.
- Health Burden: Heavy workloads, poor access to laboursaving technologies, and weak support systems lead to malnutrition and micronutrient deficiencies.
- Intergenerational Effects: Maternal undernutrition contributes to low birth weight, stunting, and poor child development.
Nutrition and Food Security
- Right to Food Framework: The National Food Security Act provides subsidised cereals, maternity entitlements, and supplementary nutrition.
- State Initiatives: Some States include millets, fortified staples, and local foods.
- Persistent Gaps: Women’s nutrition outcomes remain uneven, with high anaemia rates and cerealheavy diets.
Challenges Faced by Women Farmers
- Land Ownership Gap: Despite legal reforms, most land titles remain in men’s names due to social norms, patrilineal inheritance, and administrative hurdles.
- Exclusion from Schemes: Without formal recognition as farmers, women struggle to access credit, crop insurance, irrigation, and flagship programmes.
- Invisible Contribution: Women manage farm operations but lack recognition, leaving their labour undervalued.
Priorities for Reform
- Visibility in Law and Policy: Recognise women farmers beyond land ownership, including tenants, labourers, and tribal cultivators.
- Strengthening Land and Resource Rights: Promote joint spousal titles and incentives for registering assets in women’s names. Ensure gendersensitive land and water governance.
- NutritionFocused Food Systems: Promote pulses, millets, fruits, and vegetables through PDS, Anganwadis, and school meals.
- Access to Technology and Extension Services: Ensure women receive timely training, information, and market insights. Empower women to make informed choices on crops and sustainable practices.
Conclusion
Women farmers are central to India’s agriculture and food security, yet remain underrecognised and undersupported. Ensuring land rights, access to technology can transform their role from invisible contributors to empowered stakeholders.
MOONSHOT PROJECT
TOPIC: (GS3) SCIENCE AND TECHNOLOGY: THE HINDU
The Indian Institute of Science (IISc) has launched a Moonshot Project to develop advanced brain coprocessors.
Moonshot Project
- Objective: To design implantable and noninvasive brain coprocessors that can decode brain signals, process them using AI, and reencode them back into the brain through stimulation or feedback.
- Technology:
- AIpowered closedloop devices connecting different brain regions.
- Neuromorphic hardware mimicking brain processes.
- Origin: Evolved from a pilot project under IISc’s Brain, Computation and Data Science initiative.
- Funding: Supported by the Pratiksha Trust.
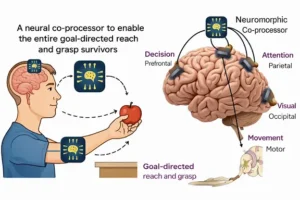
Key Features
- Brain Coprocessors: Emerging technology to enhance natural brain abilities in reallife situations.
- Multidisciplinary Approach: Involves neuroscience, AI, engineering, and medical sciences.
- Application: Focused on restoring sensorimotor functions, especially after stroke.
Significance
- Medical Impact:
- Rehabilitation of stroke survivors.
- Restoration of critical functions like goaldirected reach and grasp.
- Innovation: Firstofitskind brain coprocessor in India.
- Future Potential: Could pave the way for advanced cognitive rehabilitation and treatment of neurological disorders.
Conclusion
The Moonshot Project marks a major leap in India’s neuroscience and AI research, aiming to merge technology with medicine for human benefit and lay the foundation for future breakthroughs in neuroAI integration.
SHAHED DRONES
TOPIC: (GS3) SCIENCE AND TECHNOLOGY: THE HINDU
The United States recently expressed concern over the growing use and capabilities of Iran’s Shahed drones in global conflict zones.
Shahed Drones
- Origin: Developed by Iran; “Shahed” means witness in Farsi.
- Type: Low-cost, one-way attack drones (OWA UAVs), also called “kamikaze” or “suicide drones”.
- Function: Fly toward a target and explode on impact, acting like guided missiles.
- Variants:
- Shahed-131: Range of 700–900 km.
- Shahed-136: Longer range of 2,000–2,500 km.
- Russia refers to them as Geran-1 and Geran-2.

Key Features
- Size & Weight: Around 2.5–3 metres long; launch weight ~200 kg.
- Launch System: Uses a disposable rocket booster, followed by a piston engine.
- Navigation: Combines civilian GPS/GLONASS with inertial navigation systems (INS).
- Warheads: Can carry high-explosive, thermobaric, or shrapnel-filled munitions.
- Deployment: Can be launched from static mounts or mobile vehicles.
Strategic Significance
- Cost Advantage: Estimated cost between $20,000–$50,000, far cheaper than cruise or ballistic missiles.
- Tactical Use: Deployed in swarms to overwhelm air defences from multiple directions.
- Nickname: Often called the “poor man’s cruise missile” due to affordability and effectiveness.
Conclusion
Shahed drones represent a new era of low-cost aerial warfare. Their increasing use in global conflicts raises concerns about security, defence preparedness, and drone regulation in international defence discussions.
CONFLICT ZONES IN THE US–ISRAEL–IRAN WAR
TOPIC: (GS2) INTERNATIONAL RELATIONS: THE HINDU
The United States and Israel recently carried out joint strikes on Iran, leading to Iranian retaliation against economic targets in Gulf Cooperation Council (GCC) states.
MultiFront Conflict in West Asia
- The conflict has expanded into a multifront crisis involving state and nonstate actors.
- Strategic maritime chokepoints like the Strait of Hormuz, Red Sea, and Persian Gulf are now flashpoints, threatening global energy supplies and shipping routes.

Key State Actors
- United States & Israel: Aim to dismantle Iran’s nuclear programme and weaken its proxy networks.
- Iran: Seeks regime survival, spreads conflict regionally to raise costs for US and allies, and deter further strikes.
- GCC Nations (Saudi Arabia, UAE, Qatar, Bahrain, Kuwait, Oman): Host major US bases but face Iranian attacks on airports, oil facilities, and civilian infrastructure.
NonState Actors – “Axis of Resistance”
- Hezbollah (Lebanon): Engaged in clashes with Israel, aligned with Iran.
- Houthis (Yemen): Target commercial ships in the Red Sea and Gulf of Aden, disrupting global trade.
- Popular Mobilization Forces (Iraq): Launch strikes on US bases and Israeli interests.
- Kurdish Militias: Some supported by US and Israel as allies against Iran; Kurds remain a stateless ethnic group spread across West Asia.
Strategic Importance
- Maritime Chokepoints: Strait of Hormuz, Gulf of Oman, and Red Sea are vital for global oil trade.
- Proxy Warfare: Iran uses allied militias to expand conflict beyond its borders.
- India’s Concern: Heavy dependence on Gulf energy supplies makes stability in West Asia crucial for India’s economy and security.
Conclusion
For India, safeguarding energy imports and maritime security in these chokepoints is critical, making the region a priority in foreign policy and strategic planning.
GPS SPOOFING
TOPIC: (GS3) SCIENCE AND TECHNOLOGY: THE HINDU
Recent reports show GPS spoofing incidents affecting aircraft navigation near Iran and the UAE, creating a “digital fog of war.”
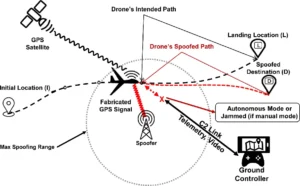
What is GPS Spoofing?
- Definition: GPS spoofing is the act of sending fake satellite signals to mislead GPS receivers.
- Purpose: It tricks devices into showing false location, speed, altitude, or time data.
- Difference from Jamming:
- Jamming blocks signals.
- Spoofing replaces real signals with fake ones.
How It Works
- Signal Manipulation: Spoofed signals are stronger than genuine ones, so receivers accept them as real.
- Aircraft Impact: Pilots may see incorrect positions on navigation systems, leading to misguided flight paths.
- Tools Used: Specialised hardware or software broadcasts counterfeit GPS signals.
Where It’s Reported
- Conflict Zones:
- Black Sea region
- West Asia and Middle East
- Areas with military operations or electronic warfare
Security Implications
- Aviation Risk: Misleading aircraft navigation can cause route errors or safety hazards.
- Military Use: Used to confuse enemy systems, disrupt operations, or mask troop movements.
- Civilian Threat: Can affect ships, drones, and vehicles, especially in sensitive zones.
Conclusion
GPS spoofing is a growing digital threat that manipulates navigation systems with false data. As its use spreads in conflict-prone regions, it poses serious risks to civilian and military operations.
DUSKY EAGLE OWL
TOPIC: (GS3) ENVIRONMENT: THE HINDU
Why in News?
A pair of rare Dusky Eagle Owls was recently sighted in the Phato tourism zone of Terai West Forest Division in Uttarakhand, near Corbett Tiger Reserve.

Physical Characteristics
- The Dusky Eagle Owl is a large and powerful owl species with a strong body and broad wings.
- Size: Approximately 48–53 cm in length, with females generally larger than males.
- Colouration:
- The body appears greyish-brown.
- Underparts are greyish-white with dark brown streaks.
- Wings are dark brown with pale streaks.
- Ear Tufts: Prominent ear-like feather tufts, which give it the characteristic eagle-owl appearance.
- Eyes: Large eyes adapted for excellent night vision.
Habitat and Behaviour
- This owl typically inhabits dense forests, riverine woodlands, and areas with large old trees.
- It prefers regions near water bodies, where prey availability is higher.
- During the daytime, it usually rests quietly in shaded branches or thick foliage to avoid disturbance.
- It becomes active around dusk and at night, although it may occasionally hunt during cloudy daylight conditions.
Feeding and Hunting Adaptations
- The species is a skilled predator with powerful talons and strong flight capability.
- It feeds mainly on:
- Small mammals such as rodents
- Birds
- Occasionally reptiles and insects
- Its sharp hearing and silent flight help it locate prey efficiently in low-light conditions.
Breeding and Nesting Behaviour
- Unlike many birds, the Dusky Eagle Owl does not build its own nest.
- Instead, it uses abandoned stick nests originally built by large birds of prey, including:
- Kites
- Vultures
- Eagles
- The nests are typically located on tall trees, providing safety from predators.
Conservation Status
- IUCN Red List: Least Concern (LC)
- Although the global population is stable, local threats include:
- Habitat loss due to deforestation
- Disturbance near nesting sites
- Decline of old-growth trees
Conservation of mature forests and riverine ecosystems is important for sustaining its population.